Most industries, including individual law firms, doctors and dentists have been keen to embrace the opportunities presented by advances in technology to maintain a competitive edge. Companies have become more digitally-enabled, and tablets, smartphones and networking sites, such as Facebook are now vital accoutrements to a successful business.
However, this increased connectivity has made businesses vulnerable to digital crime. Well resourced, intelligent cyber criminals are deploying sophisticated techniques to evade IT defenses to attain their objectives: business disruption, theft and extortion. In this article, we will discuss the three most common phishing techniques and then provide useful tips on how organizations can protect themselves.
What exactly is phishing and how does it work?
Phishing is a form of “social engineering” that attempts to steal sensitive information, such as passwords, usernames and other financial or account data. Typically, the phisher sends you an email that spoofs or mimics banks, credit companies, UPS/FedEx, or some other site for which you have login credentials. The email includes a links that directs you to a spoofed website operated by the attacker.
Once you visit the fake site, you are asked to enter account info, which may include username, password, social security number, bank account or credit card details. The spoofed site may also expose you to malware. By taking advantage of various browser vulnerabilities, the attacker may install a Trojan Horse on your computer. If done properly, the attacker can capture sensitive info without you ever knowing you have been compromised.
Why Phishing attacks are on the rise
The thing about phishing is that it is simple to implement. Forget hacking your way past one line of defense, then another, then another hoping to get the motherlode… Phishing is essentially a simple scam, a confidence trick if you will. All you have to do is setup a bogus website, craft a credible deceptive email, and send it out to millions of emails (its a little more complicated than that! but you get the idea). By comparison with hacking it is child’s play. This is why phishing has now become the #1 conveyor of malware.
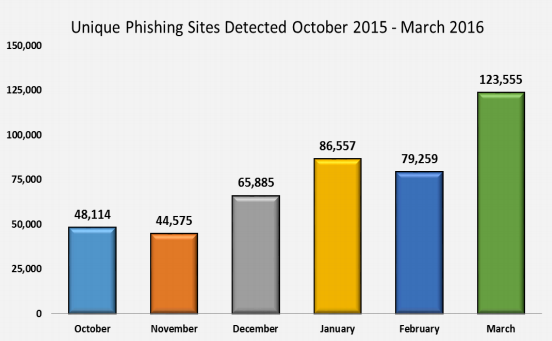
Here’s a great summary and statistics chronicling the rise of phishing attacks.
Kudos to Jonathan Crowe of security firm Barlky for pulling it together.
Phishing Techniques Used by Attackers
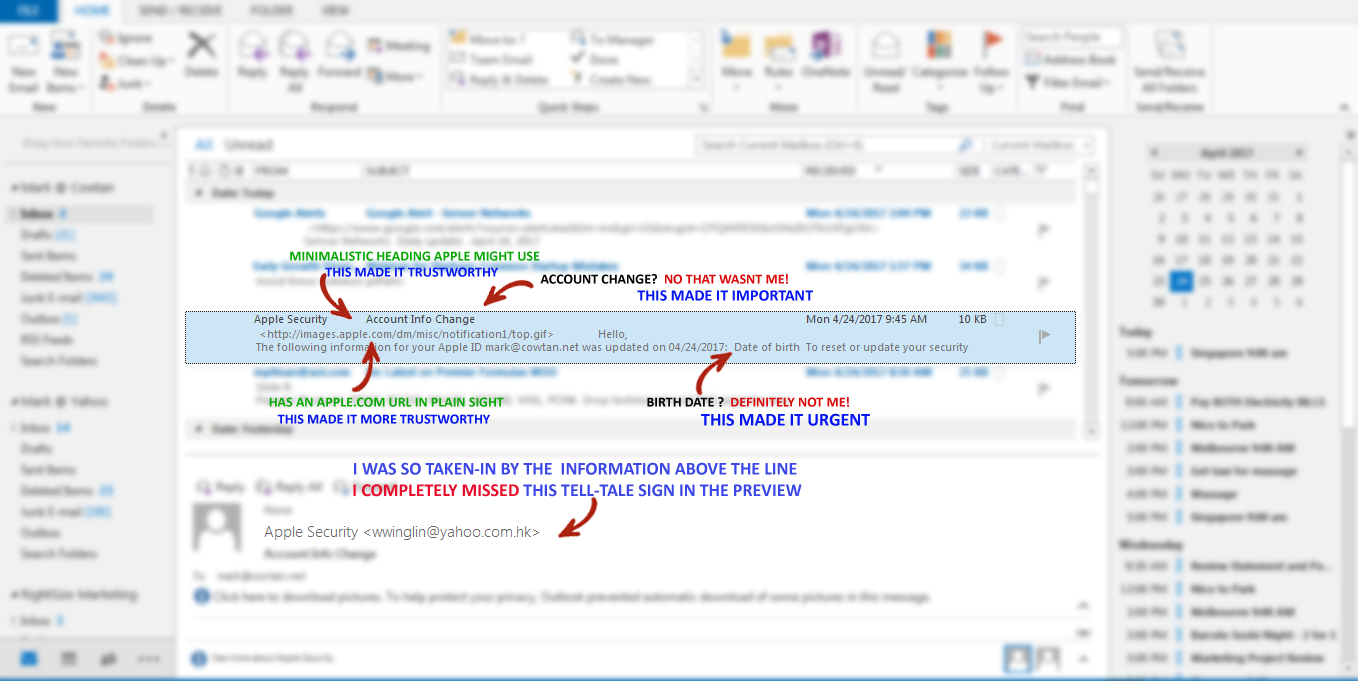
Address Spoofing: It is the most common phishing technique. The attacker creates email messages that look like they came from an authentic source. Since some email servers allow computers to connect to the Simple Mail Transfer Protocol (SMTP) port without using a password, the phisher directly connects to the email server and instructs it send messages to potential victims.
Obfuscated Links: Obfuscated links are URLs that look real, but direct a victim to the attacker’s website. Some obfuscation methods include: using HTML to present links deceptively, incorporating instruction for redirection into an otherwise legitimate URL, using alternate formats, such as hexadecimal to represent the URL and using international domain name registration or misspelled version of the spoofed site to recreate the target URL.
HTML: Some phishing messages may appear real. To enable these messages to bypass anti-spam software, phishers may include HTML markup containing instructions and invisible words.
DNS cache poisoning: This occurs when the attacker successfully changes a company’s DNS server information, and makes everyone trying to access a legitimate site to be redirected to a fake site.
Key Loggers and Trojans: Phishers also use malicious programs in their scams. For example, keyloggers and screen capture Trojans gather and report info about a victim to the phisher. Spyware can be used to track and record your online behavior, enabling the phisher to plan other attacks. Bots can be used to maintain fabricated conversation with the victim in coordinate zombie networks or chat rooms.
“Social Engineering” and Phishing
You may have heard the buzzword Social Engineering and wondered what it means. It is a term used to refer to the different malicious activities achieved through human interactions. It entails psychological manipulation to trick victims in giving away sensitive information or making security mistakes. Since social engineering involves hacking human emotions, there are many ways an attacker can extract data from their victims. Phishing scams are one of the most popular manifestations of social engineering tactics. They are designed to create a sense of curiosity, urgency or fear in victims and then prod them to reveal sensitive info, open attachments that contain malware or click on links to malicious sites. Other common social engineering techniques include baiting, scareware and pretexting.
Understanding Spear Phishing
Spear Phishing is a highly targeted form of phishing attack that focuses on specific individuals or organizations, rather than just anyone. Spear phishers typically use personal information that is specific to you so as to gain your trust and appear more legitimate. In most cases, this information is taken from your social media accounts and other online activities.
An organizational spear phishing attack scenario may involve an attacker impersonating an organization’s IT consultant, and sends emails to one or more employees prompting them to change their passwords and provides them a link to a malicious page where the phisher captures their credentials. The emails are worded and signed just as the consultant normally does; thereby deceiving the employees into thinking it is a legitimate message.
Five Countermeasures to Prevent Phishing Attacks
1. Keep Antivirus/Anti-malware Software Updated
Ensure automatic updates are enabled or make it a habit to regularly download the latest signature files. Check updates periodically to be sure they have been applied and can protect your system for possible infections.
2. Use Multi-factor Authentication
One of the most important pieces of information phishers look for is the victim’s credentials. Using a multi-factor authentication is one of the most powerful ways to authenticate the true identity of users and it helps you to protect account security, even in the event of system compromise.
3. User Education and Vigilance
There is no substitute for awareness and human vigilance. Educate your employees and carry out training sessions with mock phishing scenarios. Though there are a plethora of reliable educational resources on the internet designed to assist people in avoiding phishing attacks, it is recommended you hire an experienced IT specialist to do the training, they will be able to answer all the questions that arise, and present them in the context of your setup.
4. Confirm Address Bar Reads “HTTPS”
Before sharing any confidential information online, check your address bar to verify it reads “HTTPS” and not the standard” HTTP”. The “S” means that your information is being conveyed in an authentic and secure website, and that it is encrypted in transit, so in cannot be decoded by someone “sniffing” your connection to that site.
5. Set up a Central Inbox
Consider setting up one email address where all suspected phishing emails are directed, with an address, such as [email protected] or [email protected]. Monitor this central inbox 24/7. The best way to discover if your business is being targeted by phishers is by providing users an easy way to report reporting suspicious email and attacks to your IT department, who can subsequently block access to the bogus sites.